Current Default: Nginx 1.31.1
Default across all branches (132.00stable, 140.00beta01, 141.00beta01).
Latest Upstream: Mainline ... | Stable ...
Centmin Mod Nginx Install Path
Centmin Mod installs Nginx to /usr/local/nginx/ (not /etc/nginx/). Main config: /usr/local/nginx/conf/nginx.conf. Vhost configs: /usr/local/nginx/conf/conf.d/.
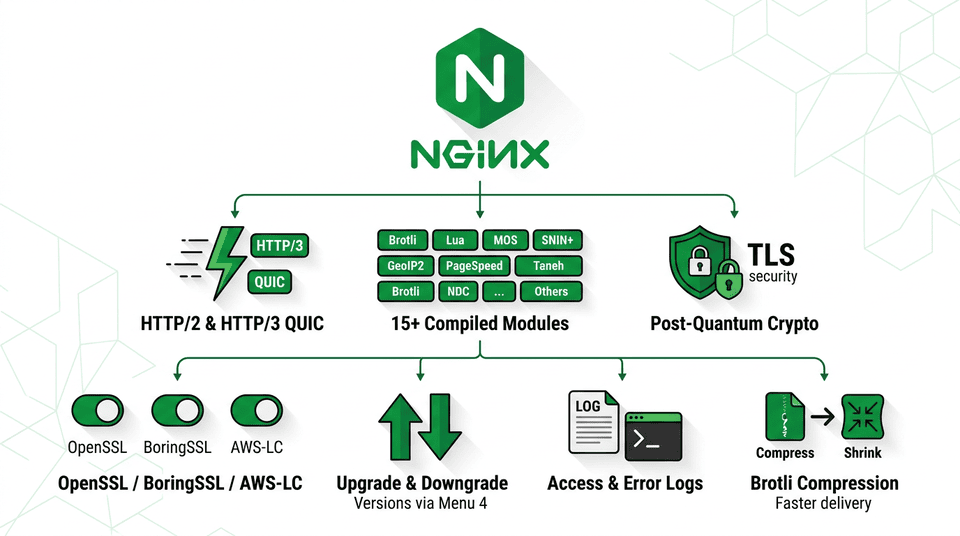
Centmin Mod installs Nginx 1.31.1 by default across all branches - no configuration is needed. To install a different Nginx version, set NGINX_VERSION in /etc/centminmod/custom_config.inc before running the initial Centmin Mod installer. To upgrade or downgrade Nginx after installation, run centmin.sh menu option 4.
HTTP/2 & HTTP/3 QUIC Support
HTTP/2 is enabled by default in all Centmin Mod Nginx builds via the NGINX_HTTP2='y' compile-time variable - no configuration needed. It includes HPACK header compression for faster page loads.
HTTP/3 is a newer protocol that uses QUIC (a UDP-based transport) instead of TCP. It provides faster initial connections, better performance on mobile networks and high-latency links, and eliminates head-of-line blocking that can slow down HTTP/2. Enable HTTP/3 QUIC by setting NGINX_QUIC_SUPPORT='y' before Nginx compilation, and opening UDP port 443 in your firewall (e.g., add 443 to UDP_IN and UDP_OUT in /etc/csf/csf.conf if using CSF).
Note: Nginx still considers HTTP/3 QUIC support experimental. It works well in practice but is not yet marked as stable by the Nginx project.
For historical reference on the original HTTP/2 transition from SPDY in Nginx 1.9.5 (2015), including migration steps and benchmarks, see the Nginx HTTP/2 Protocol archive page.
Quick Start: Recommended Setup (AWS-LC)
Recommended: AWS-LC
AWS-LC is the recommended crypto library for HTTP/3 QUIC. Developed and maintained by Amazon for use in their own production infrastructure (AWS), it receives frequent updates and security patches. AWS-LC provides HTTP/3 QUIC support plus post-quantum cryptography (protects against future quantum computer attacks) and FIPS 140-3 compliance (required by government and financial industry regulations).
Add the following line to /etc/centminmod/custom_config.inc, then run centmin.sh menu option 4 to recompile Nginx. If you’re doing a fresh Centmin Mod installation, add it before running the installer:
AWS_LC_SWITCH='y'
AWS-LC Trade-offs
- Lua modules disabled - AWS-LC is not compatible with OpenResty Lua modules (Lua Nginx and Lua Stream). If your Nginx configuration relies on Lua scripting (e.g., custom request handling or WAF rules), use quicTLS instead.
- EL7 not supported - AWS-LC only works on EL8, EL9, and EL10 (AlmaLinux/Rocky Linux 8, 9, 10). CentOS 7 (EL7) users should use quicTLS.
- Requires Nginx 1.27.0+ - The current Centmin Mod default (Nginx 1.31.1) meets this requirement.
Alternative Crypto Libraries for HTTP/3
If AWS-LC doesn’t suit your needs (for example, you need Lua modules or you’re on CentOS 7), two other libraries also provide HTTP/3 support:
| Library | custom_config.inc Variable |
Best For | What You Give Up |
|---|---|---|---|
| AWS-LC Recommended | AWS_LC_SWITCH='y' |
Most features: HTTP/3 + post-quantum crypto + FIPS. Actively maintained by Amazon | No Lua modules; EL8, EL9, EL10 only (no EL7); needs Nginx ≥ 1.27.0 |
| quicTLS | NGINX_QUIC_SUPPORT='y' |
Simplest option - all Nginx modules work, including Lua. Works on all OS versions including EL7 | Based on OpenSSL 1.1.1 (end-of-life - no upstream security patches); no post-quantum crypto |
| BoringSSL | BORINGSSL_SWITCH='y' |
Post-quantum crypto support; maintained by Google | OCSP stapling disabled (may slow certificate verification); set-misc-nginx module incompatible; no FIPS compliance |
Only One at a Time
You can only use one crypto library at a time - they are mutually exclusive. If you accidentally enable both AWS-LC and quicTLS in your config, Centmin Mod automatically picks AWS-LC on EL8/EL9/EL10 servers. Priority order: LibreSSL > BoringSSL > AWS-LC > quicTLS.
Configuring Your Nginx Vhosts for HTTP/3
Manual Configuration Required
Recompiling Nginx with a QUIC library is only the first step. You also need to manually edit each website’s Nginx vhost configuration file to enable HTTP/3. Centmin Mod’s vhost templates do not add these directives automatically.
Your existing vhost config file (typically at /usr/local/nginx/conf/conf.d/yourdomain.com.ssl.conf) already contains listen lines for HTTPS over TCP. To enable HTTP/3, add new listen lines for QUIC over UDP, plus a header that tells browsers your site supports HTTP/3.
First vhost on this IP:port - with reuseport:
# Existing HTTPS (TCP) listeners - already in your vhost
listen 443 ssl http2;
listen [::]:443 ssl http2;
# Add these lines for HTTP/3 (UDP) - reuseport on first vhost only
listen 443 quic reuseport;
listen [::]:443 quic reuseport;
# Tell browsers that HTTP/3 is available on this site
add_header Alt-Svc 'h3=":$server_port"; ma=86400';
What is reuseport?
The reuseport keyword is a Linux kernel feature that distributes incoming connections across multiple Nginx worker processes for better performance. You should only add reuseport on the first vhost that uses a given IP address and port. If you have multiple websites on the same server, only the first one gets reuseport.
Additional vhosts on the same IP:port - without reuseport:
# Additional vhosts on the same IP - no reuseport
listen 443 quic;
listen [::]:443 quic;
add_header Alt-Svc 'h3=":$server_port"; ma=86400';
After editing your vhost files, test the configuration and restart Nginx:
nginx -t && service nginx restart
For a detailed step-by-step walkthrough, see the community forum guide: How to Enable Centmin Mod Nginx HTTPS HTTP/3 QUIC Support.
Firewall: UDP Port 443
Regular HTTPS uses TCP port 443. HTTP/3 additionally uses UDP port 443. If your firewall blocks UDP traffic on port 443, HTTP/3 connections will silently fail and browsers will fall back to HTTP/2.
CSF Firewall Users: No Action Needed
If you use CSF firewall (Centmin Mod’s default), this is handled automatically. When you enable a QUIC-capable crypto library, Centmin Mod adds UDP port 443 to CSF’s allowed ports (UDP_IN, UDP_OUT, UDP6_IN, UDP6_OUT in /etc/csf/csf.conf).
For non-CSF firewall setups, manually open UDP port 443:
# firewalld (EL8/EL9/EL10)
firewall-cmd --permanent --add-port=443/udp
firewall-cmd --reload
# iptables
iptables -A INPUT -p udp --dport 443 -j ACCEPT
ip6tables -A INPUT -p udp --dport 443 -j ACCEPT
Verifying HTTP/3 Is Working
After completing the steps above, verify that HTTP/3 is properly configured.
Step 1: Check Nginx compilation - Confirm the HTTP/3 module was compiled into Nginx:
nginx -V 2>&1 | grep http_v3_module
If you see --with-http_v3_module in the output, HTTP/3 support is compiled in.
Step 2: Test from command line - Use curl to make an HTTP/3 request (requires curl 7.88+ with HTTP/3 support):
curl --http3 -I https://yourdomain.com
Look for HTTP/3 200 in the response. If you see HTTP/2 200 instead, HTTP/3 is not being used - check your vhost config and firewall.
Step 3: Browser verification - In Chrome, open DevTools (F12) → Network tab → right-click the column headers → enable “Protocol”. Reload your page - HTTP/3 connections show as h3.
First Visit Uses HTTP/2
Browsers negotiate HTTP/3 automatically. On the first visit, the browser connects via HTTP/2 and learns about HTTP/3 from the Alt-Svc header. On subsequent visits, it upgrades to HTTP/3. This means you may need to reload the page twice to see h3 in DevTools.
Experimental Status
Nginx officially considers HTTP/3 QUIC support experimental. While it works reliably in production for many users, it has not yet been marked as stable by the Nginx project. Test thoroughly before deploying to high-traffic production environments.
TLS 1.3 Required
HTTP/3 requires TLS 1.3, which is already the default in all Centmin Mod Nginx builds. No additional TLS configuration is needed.
Enabled Modules (Default)
These modules are compiled and enabled by default in every Centmin Mod Nginx build:
| Module | Type | Description |
|---|---|---|
| http_v2_module | Static | HTTP/2 protocol with HPACK encoding |
| http_ssl_module | Static | HTTPS/TLS support |
| http_realip_module | Static | Real IP detection behind proxies/CDN |
| http_stub_status_module | Static | Server statistics and monitoring |
| http_sub_module | Static | Response body string substitution |
| http_addition_module | Static | Append/prepend text to responses |
| http_gzip_static_module | Static | Pre-compressed static file serving |
| ngx_cache_purge | Static | FastCGI/proxy cache purge support |
| ngx_http_redis | Static | Redis protocol support for caching |
| ngx_fancyindex | Dynamic | Fancy directory listing |
| headers-more | Dynamic | Set/clear input and output headers |
| ngx_brotli | Dynamic | Brotli compression (on-the-fly & static) |
| ngx_image_filter | Dynamic | On-the-fly image resizing/cropping |
| set-misc-nginx | Dynamic | Extended set directives (base64, hashing) |
| echo-nginx | Dynamic | Shell-style echo/sleep/time in configs |
| lua-nginx-module | Dynamic | OpenResty Lua scripting engine |
| ngx_devel_kit | Dynamic | Development kit for 3rd-party modules |
| GeoIP (legacy) | Static | MaxMind GeoIP country/city lookups |
| http_secure_link_module | Static | URL verification via hashed links |
| stream_module | Static | TCP/UDP proxy and load balancing (with stream_ssl) |
| stream_ssl_preread_module | Static | SSL/TLS info extraction without terminating |
Disabled/Optional Modules
These modules can be enabled via /etc/centminmod/custom_config.inc before running centmin.sh menu option 4 to recompile Nginx, or before initial Centmin Mod installation:
| Module | Variable | Description |
|---|---|---|
| PageSpeed (Deprecated) | NGINX_PAGESPEED='y' | Google PageSpeed optimization module (Deprecated - no longer supported) |
| WebDAV | NGINX_WEBDAV='y' | WebDAV protocol support |
| RTMP | NGINX_RTMP='y' | RTMP live streaming |
| njs | NGXDYNAMIC_NJS='y' | Nginx JavaScript scripting |
| GeoIP2 | NGINX_GEOIPTWOLITE='y' | MaxMind GeoIP2 Lite database support |
| ModSecurity | NGINX_MODSECURITY='y' | Web application firewall (WAF) |
| VTS | NGINX_VHOSTSTATS='y' | Virtual host traffic status monitoring |
| testcookie | NGXDYNAMIC_TESTCOOKIE='y' | Bot detection via test cookie |
| HTTP Concat | NGINX_HTTPCONCAT='y' | Concatenate CSS/JS files (Alibaba) |
| srcache | NGXDYNAMIC_SRCCACHE='y' | Transparent subrequest-based caching |
| memc-nginx | NGXDYNAMIC_MEMC='y' | Extended Memcached interface |
| redis2 | NGXDYNAMIC_REDISTWO='y' | Full Redis 2.0 protocol support |
| zstd | NGXDYNAMIC_ZSTD='y' | Zstandard compression |
| http_auth_request | NGINX_AUTHREQ='y' | Subrequest-based client authorization |
| nginx-length-hiding | NGINX_LENGTHHIDE='y' | BREACH attack mitigation |
| XSLT | NGINX_XSLT='y' | XML/XSLT response transformations |
| Perl | NGINX_PERL='y' | Embedded Perl scripting |
| FLV | NGINX_FLV='y' | Flash Video pseudo-streaming |
| MP4 | NGINX_MP4='y' | MP4 pseudo-streaming with seek |
| Slice | NGINX_SLICE='y' | Split large responses for caching |
| Passenger | NGINX_PASSENGER='y' | Phusion Passenger app server |
GeoIP2 Lite Module
The GeoIP2 module (ngx_http_geoip2_module) allows Nginx to use MaxMind GeoLite2 databases for country, city, and ASN lookups based on client IP. This enables geo-based access control, content localization, and analytics directly at the web server level. To enable GeoIP2, set NGINX_GEOIPTWOLITE='y' in /etc/centminmod/custom_config.inc, recompile Nginx via menu option 4, GeoLite2 databases are downloaded automatically from Centmin Mod's own mirror - no MaxMind account is needed. Optionally, you can set MM_LICENSE_KEY for direct MaxMind downloads.
Enabling the Module
Add the following to /etc/centminmod/custom_config.inc and then recompile Nginx via menu option 4:
# Add to /etc/centminmod/custom_config.inc
NGINX_GEOIPTWOLITE='y'
NGXDYNAMIC_GEOIPTWOLITE='y'
# MaxMind license key is OPTIONAL - Centmin Mod downloads GeoLite2
# databases from its own mirror by default (no account needed).
# Only set MM_LICENSE_KEY if you prefer direct MaxMind downloads:
# MM_LICENSE_KEY='your_maxmind_license_key_here'Setting NGXDYNAMIC_GEOIPTWOLITE='y' compiles the module as a dynamic (loadable) module. Both variables default to 'n' (disabled). Note: A MaxMind license key (MM_LICENSE_KEY) is optional. By default, Centmin Mod downloads GeoLite2 databases from its own mirror - no MaxMind account or license key is needed. If you prefer direct MaxMind downloads, you can optionally set your own free MaxMind license key in /etc/centminmod/custom_config.inc (see MaxMind License Key section below).
MaxMind License Key (Optional)
By default, Centmin Mod downloads GeoLite2 databases from its own mirror - no MaxMind account or license key is needed. If you prefer direct MaxMind downloads, you can optionally set your own free MaxMind license key in /etc/centminmod/custom_config.inc:
MM_LICENSE_KEY='your_maxmind_license_key_here'Database Paths
GeoLite2 databases are stored in /usr/share/GeoIP/ and include GeoLite2-Country, GeoLite2-City, and GeoLite2-ASN databases.
Nginx Configuration
After enabling and recompiling, configure GeoIP2 in your Nginx config:
# In nginx.conf http{} block
geoip2 /usr/share/GeoIP/GeoLite2-Country.mmdb {
$geoip2_country_code country iso_code;
$geoip2_country_name country names en;
}
geoip2 /usr/share/GeoIP/GeoLite2-City.mmdb {
$geoip2_city_name city names en;
$geoip2_region_name subdivisions 0 names en;
}
# Block specific countries in a server{} block
if ($geoip2_country_code = "XX") {
return 403;
}PHP Integration
Pass GeoIP2 data to PHP via fastcgi_param directives in your Nginx vhost config:
# In your vhost PHP location block
fastcgi_param GEOIP_COUNTRY_CODE $geoip2_country_code;
fastcgi_param GEOIP_COUNTRY_NAME $geoip2_country_name;
fastcgi_param GEOIP_CITY_NAME $geoip2_city_name;These values are then accessible in PHP via $_SERVER['GEOIP_COUNTRY_CODE'], etc.
GeoIP2 Automatic Database Updates via Cron
When the GeoIP2 module is enabled, Centmin Mod automatically installs a cron job (tools/geoip2db-update.sh) that runs weekly on Thursdays at 2:20 AM to download updated MaxMind GeoLite2 databases (GeoLite2-Country, GeoLite2-City, and GeoLite2-ASN) to /usr/share/GeoIP/. This ensures your MaxMind geolocation data stays current without manual intervention.
For firewall-level country blocking (blocking at the network layer before requests reach Nginx), see CSF Country-Based IP Blocking. Nginx-level GeoIP2 blocking is useful when behind Cloudflare, where real client IPs are visible to Nginx but not to iptables.
For more details and discussion, see the community forum thread.
Post-Quantum Key Exchange (PQ KEX)
Post-quantum key exchange protects the TLS handshake against future cryptographically-relevant quantum computers. Today’s asymmetric key exchange algorithms (like ECDH/X25519) could be broken by a sufficiently powerful quantum computer, enabling “harvest now, decrypt later” attacks where adversaries record encrypted traffic today and decrypt it once quantum hardware matures. Centmin Mod Nginx supports hybrid PQ KEX algorithms - X25519MLKEM768 and X25519Kyber768Draft00 - which combine classical X25519 with a post-quantum algorithm so the connection remains secure even if one component is broken. Cloudflare already supports PQ KEX at their edge; enabling it on the origin ensures the full Cloudflare ↔ origin path is post-quantum safe. See also: Centmin Mod PQ KEX guide, post-quantum for all, and state of PQ internet 2025.
Requirements
- TLS 1.3 must be enabled (default in Centmin Mod)
- BoringSSL (
BORINGSSL_SWITCH='y') - all supported EL versions (EL7/EL8/EL9/EL10) - AWS-LC (
AWS_LC_SWITCH='y') - EL8/EL9/EL10 only, requires Nginx 1.27.0+ - Set the variable in
/etc/centminmod/custom_config.inc, then rebuild Nginx via centmin.sh menu option 4, or set before initial Centmin Mod installation
Two PQ Curve Options
- X25519MLKEM768 - Newer NIST ML-KEM standard (FIPS 203). Recommended for new deployments.
- X25519Kyber768Draft00 - Older IETF hybrid draft. Use for broader client compatibility or legacy deployments.
Step 1 - Enable BoringSSL or AWS-LC
Set one of the following in /etc/centminmod/custom_config.inc before running centmin.sh menu option 4 to recompile Nginx, or before initial Centmin Mod installation (they are mutually exclusive):
BORINGSSL_SWITCH='y'
AWS_LC_SWITCH='y'
Step 2 - Configure ssl_ecdh_curve
Add to the http {} block in /usr/local/nginx/conf/nginx.conf (or per virtual host):
ssl_ecdh_curve X25519MLKEM768:X25519;
ssl_ecdh_curve X25519Kyber768Draft00:X25519;
Step 3 - Cloudflare Origin Opt-In (Optional)
If your site is behind Cloudflare, opt the zone into post-quantum encryption to the origin via the Cloudflare API:
curl -s -X PUT "https://api.cloudflare.com/client/v4/zones/{zone_id}/cache/origin_post_quantum_encryption" \
-H "Authorization: Bearer $CF_API_TOKEN" \
-H "Content-Type: application/json" \
--data '{"value": "preferred"}'
Valid values: supported (attempt PQ, fall back), preferred (strongly prefer PQ), off.
Step 4 - Verify
After rebuilding Nginx via Menu 4, confirm the SSL library is active:
nginx -t && nginx -V 2>&1 | grep -E '(BoringSSL|AWS-LC|OpenSSL)'
The output will show built with BoringSSL or built with AWS-LC confirming PQ KEX capability.
Incompatibilities & Limitations
- BoringSSL: OCSP stapling is disabled (expected behavior). Incompatible with the
set-misc-nginxmodule. - AWS-LC: EL8/EL9/EL10 only; requires Nginx 1.27.0+. Incompatible with OpenResty Lua modules.
- Both: Mutually exclusive with each other and with quicTLS (
NGINX_QUIC_SUPPORT='y'). Only one SSL library can be active at a time.
Crypto Library Support Matrix
Centmin Mod supports six different SSL/crypto libraries for Nginx, each offering different trade-offs. Multiple options exist because mainstream OpenSSL has historically lagged behind on HTTP/3 QUIC support, post-quantum key exchange, and performance optimizations. Having alternatives also provides security resilience - if one library has a vulnerability and patches are slow, you can quickly switch to another to reduce your exposure window.
Library Overview
Set the desired variable in /etc/centminmod/custom_config.inc before running centmin.sh menu option 4 to recompile Nginx, or before initial Centmin Mod installation.
| Library | Variable | Version | Description |
|---|---|---|---|
| System OpenSSL | OPENSSL_SYSTEM_USE='y' |
OS-provided | Uses the operating system’s packaged OpenSSL. Default for EL8/EL9/EL10. |
| OpenSSL (source) | NOSOURCEOPENSSL='n' |
1.1.1w | Source-compiled OpenSSL 1.1.1w. Default for EL7. Full module compatibility. |
| quicTLS | NGINX_QUIC_SUPPORT='y' |
1.1.1w+quic | OpenSSL fork with QUIC API for HTTP/3 support. Full module compatibility. |
| BoringSSL | BORINGSSL_SWITCH='y' |
Latest | Google’s OpenSSL fork. HTTP/3 QUIC + Post-Quantum Key Exchange. |
| AWS-LC | AWS_LC_SWITCH='y' |
1.60.0 (1.37.0 in 132.00stable) | Amazon’s crypto library. HTTP/3 + PQ KEX + FIPS 140-3 validated. |
| LibreSSL | LIBRESSL_SWITCH='y' |
3.9.2 | OpenBSD’s security-focused OpenSSL fork. |
OS & Branch Compatibility
Not every library is available on every OS or branch. EL10 support requires branch 141.00beta01.
| Library | EL7 | EL8 | EL9 | EL10 |
|---|---|---|---|---|
| System OpenSSL | 1.0.2k (via openssl11) | Default 1.1.1k | Default 3.0.7 | Default 3.5.x |
| OpenSSL 1.1.1w (source) | Default | ✓ | ✓ | ✓ |
| quicTLS | ✓ | ✓ | ✓ | ✓ (141 only) |
| BoringSSL | ✓ | ✓ | ✓ | ✓ (141 only) |
| AWS-LC | ✗ | ✓ (140/141) | ✓ (140/141) | ✓ (141 only) |
| LibreSSL | ✓ | ✓ | ✓ | ✓ (141 only) |
Default Behavior
- EL7 - Source-compiled OpenSSL 1.1.1w (system OpenSSL 1.0.2k is too old for TLS 1.3)
- EL8/EL9/EL10 - System OpenSSL via
OPENSSL_SYSTEM_USE='y'
No configuration is needed for the default - it works out of the box. Only change the crypto library if you need HTTP/3 QUIC, Post-Quantum Key Exchange, or FIPS compliance.
Mutually Exclusive - Only One Library at a Time
Only one crypto library can be active. If multiple are set, this priority order applies:
- LibreSSL - Forces
OPENSSL_SYSTEM_USE='n', disables Lua modules - BoringSSL - Forces
OPENSSL_SYSTEM_USE='n' - AWS-LC - Takes priority over quicTLS, forces
NGINX_QUIC_SUPPORT='n', disables Lua - quicTLS - Forces
AWS_LC_SWITCH='n'
Module Compatibility
Some crypto libraries disable certain Nginx modules. Check this table before switching.
| Library | OpenResty Lua | set-misc-nginx | OCSP Stapling | HTTP/3 QUIC |
|---|---|---|---|---|
| System OpenSSL | ✓ | ✓ | ✓ | ✗ |
| OpenSSL 1.1.1w | ✓ | ✓ | ✓ | ✗ |
| quicTLS | ✓ | ✓ | ✓ | ✓ |
| BoringSSL | ✓ | ✗ | ✗ | ✓ |
| AWS-LC | ✗ | ✓ | ✓ | ✓ |
| LibreSSL | ✗ | ✓ | ✓ | ✗ |
Strengths & Trade-offs
System OpenSSL
Pros: Zero maintenance, automatic OS security patches, broadest compatibility. Cons: Version locked to OS release cycle, no HTTP/3 QUIC support.
OpenSSL 1.1.1w (source)
Pros: Full TLS 1.3, full module compatibility, stable and well-tested. Cons: End-of-life (no upstream patches), no HTTP/3 QUIC.
quicTLS
Pros: HTTP/3 QUIC support, full module compatibility, drop-in upgrade from OpenSSL. Cons: Based on EOL OpenSSL 1.1.1, no post-quantum key exchange.
BoringSSL
Pros: HTTP/3 QUIC + Post-Quantum KEX, actively maintained by Google, proven at scale. Cons: OCSP stapling disabled, set-misc-nginx module incompatible.
AWS-LC
Pros: HTTP/3 QUIC + PQ KEX + FIPS 140-3 validated, Amazon-maintained. Cons: EL8, EL9, EL10 only (no EL7), requires Nginx 1.27.0+, OpenResty Lua modules disabled.
LibreSSL
Pros: Security-focused design from OpenBSD, clean modern API. Cons: OpenResty Lua modules disabled, no HTTP/3 QUIC, smaller community.
Quick Reference
Add one of these lines to /etc/centminmod/custom_config.inc before running centmin.sh menu option 4 to rebuild Nginx, or before initial Centmin Mod installation:
# System OpenSSL (default on EL8/EL9/EL10)
OPENSSL_SYSTEM_USE='y'
# Source-compiled OpenSSL 1.1.1w (default on EL7)
NOSOURCEOPENSSL='n'
# quicTLS - HTTP/3 QUIC support
NGINX_QUIC_SUPPORT='y'
# BoringSSL - HTTP/3 + Post-Quantum KEX
BORINGSSL_SWITCH='y'
# AWS-LC - HTTP/3 + PQ KEX + FIPS (EL8+ only)
AWS_LC_SWITCH='y'
# LibreSSL 3.9.2 - security-focused (disables Lua)
LIBRESSL_SWITCH='y'
BoringSSL TLS 1.3
BoringSSL is Google’s fork of OpenSSL that provides TLS 1.3 support with post-quantum key exchange. To enable BoringSSL, set BORINGSSL_SWITCH='y' in /etc/centminmod/custom_config.inc.
Then update Centmin Mod and recompile Nginx:
BORINGSSL_SWITCH='y'
# Update Centmin Mod code first
cmupdate
# Then run centmin.sh and select menu option 4 to recompile Nginx
centmin.sh
BoringSSL requires Nginx 1.15.3 or newer (the current Centmin Mod default of Nginx 1.31.1 meets this requirement).
Important BoringSSL Limitations
- BoringSSL does NOT support OCSP stapling - this may slow down TLS certificate verification for some clients.
- BoringSSL does NOT support dual RSA+ECDSA certificate configurations.
- BoringSSL is incompatible with the
set-misc-nginxmodule. - Alternative: If you need OCSP stapling or dual certificates, use OpenSSL 1.1.1+ or AWS-LC instead, which support TLS 1.3 with a full feature set.
To switch back to OpenSSL, set BORINGSSL_SWITCH='n' in /etc/centminmod/custom_config.inc and recompile Nginx via centmin.sh menu option 4.
For more details, see the forum discussion.
OpenResty Lua Module
Centmin Mod includes the OpenResty Lua Nginx module as a dynamic module (NGINX_OPENRESTY='y'). This is enabled by default. To override, set the variable in /etc/centminmod/custom_config.inc before running centmin.sh menu option 4 or before initial Centmin Mod installation. This embeds LuaJIT into Nginx for high-performance scripting directly in your Nginx configuration.
Companion OpenResty modules included:
- set-misc-nginx-module - Extended set directives (base64, hashing, random)
- echo-nginx-module - Shell-style echo, sleep, time in configs
- ngx_devel_kit - Development kit for third-party modules
Dynamic modules are loaded in /usr/local/nginx/conf/dynamic-modules.conf and can be individually enabled or disabled.
Brotli Compression
Brotli compression is compiled as a dynamic module (NGXDYNAMIC_BROTLI='y'), enabled by default. To override, set the variable in /etc/centminmod/custom_config.inc before running centmin.sh menu option 4 or before initial Centmin Mod installation. It provides 15-25% better compression than gzip for text-based content. It supports both on-the-fly compression and serving pre-compressed .br files.
For image optimization, Nginx can also conditionally serve WebP format images to supported browsers, providing up to 80% file size reduction over JPG/PNG.
HTTP Concat Module
The nginx-http-concat module (by Alibaba) concatenates multiple CSS or JavaScript files into a single response, reducing HTTP requests. It is disabled by default.
Enable it with NGINX_HTTPCONCAT='y' in /etc/centminmod/custom_config.inc before running centmin.sh menu option 4 to recompile Nginx, or before initial Centmin Mod installation.
Usage Example
Request multiple files in one URL:
https://example.com/??style1.css,style2.css,style3.css
Nginx Upgrade / Downgrade (Menu 4)
Use centmin.sh menu option 4 to upgrade or downgrade Nginx after Centmin Mod is already installed. This recompiles Nginx from source with all your configured modules. Menu option 4 is for post-install upgrades only - for the initial installation, Centmin Mod installs Nginx 1.31.1 by default, or you can set NGINX_VERSION in /etc/centminmod/custom_config.inc before running the installer to use a different version.
# To upgrade/downgrade Nginx after installation,
# set the desired version in custom_config.inc
NGINX_VERSION='1.31.1'
# Then run centmin.sh and select option 4
centmin.sh
--------------------------------------------------------
Centmin Mod Menu 141.00beta01 centminmod.com
--------------------------------------------------------
1). Centmin Install
2). Add Nginx vhost domain
3). NSD setup domain name DNS
4). Nginx Upgrade / Downgrade
5). PHP Upgrade / Downgrade
6). MySQL User Database Management
7). Persistent Config File Management
8). PostgreSQL Server Management
9). Option Being Revised (TBA)
10). Memcached Server Re-install
11). MariaDB MySQL Upgrade & Management
12). Zend OpCache Install/Re-install
13). Install/Reinstall Redis PHP Extension
14). SELinux disable
15). Install/Reinstall ImagicK PHP Extension
16). Change SSHD Port Number
17). Multi-thread compression: zstd,pigz,pbzip2,lbzip2
18). Suhosin PHP Extension install
19). Install FFMPEG and FFMPEG PHP Extension
20). NSD Install/Re-Install
21). Data Transfer
22). Add Wordpress Nginx vhost + Cache Plugin
23). Update Centmin Mod Code Base
24). Exit
--------------------------------------------------------
Enter option [ 1 - 24 ] 4
--------------------------------------------------------
**********************************************************************
* Nginx Update script - Included in Centmin Extras
* Version: 141.00beta01.b161 - Date: 16/08/25 - Copyright 2011-2025 CentminMod.com
**********************************************************************
This software comes with no warranty of any kind. You are free to use
it for both personal and commercial use as licensed under the GPL.
Nginx Upgrade - Would you like to continue? [y/n] y
Current Nginx Version: 1.31.1 (100326-200708-almalinux10-virtualbox-kvm-673b155)
Install which version of Nginx? (version i.e. type 1.31.1): 1.31.1
Do you still want to continue? [y/n] y
Editing Configs the Right Way
Always set configuration variables in /etc/centminmod/custom_config.inc (shortcut: customconfig) rather than editing centmin.sh directly. This persists your settings across Centmin Mod updates.
Auto-Backup on Upgrade
Before each Nginx upgrade, Centmin Mod automatically backs up your Nginx directory to /usr/local/nginxbackup. This allows you to restore your previous Nginx installation if needed.
Persistent Config File Management (Menu 7)
Menu option 7 manages persistent configuration files. Additionally, the Nginx VTS (Virtual Host Traffic Status) module can be optionally enabled to provide real-time traffic statistics per virtual host including request counts, response times, and bandwidth usage.
Enable VTS with NGINX_VHOSTSTATS='y' and recompile via Menu 4.
Access & Error Logs
Nginx log files in Centmin Mod include the Centmin Mod main server logs, default virtual host logs, and per-vhost (per-domain) logs:
Centmin Mod Main Nginx Log Paths
/usr/local/nginx/logs/error.log- Centmin Mod main Nginx error log (compiled-in default)/usr/local/nginx/logs/access.log- Centmin Mod main Nginx access log (compiled-in default)
Default Virtual Host & Per-Domain Log Paths
/var/log/nginx/error.log- Default virtual host error log/var/log/nginx/access.log- Default virtual host access log/home/nginx/domains/domain.com/log/access.log- Per-vhost access log/home/nginx/domains/domain.com/log/error.log- Per-vhost error log
Log rotation is handled automatically via logrotate with daily rotation and 10 days of retention.
JSON-Based Access Logging
Centmin Mod supports JSON-formatted access logs for easier parsing and analysis. The log_format main_json format is already defined in the base /usr/local/nginx/conf/nginx.conf template - you do not need to add it manually.
Do NOT add log_format manually
The log_format main_json block is already included in the default nginx.conf template. Adding it again will cause an Nginx configuration error due to duplicate log format names.
To enable JSON logging for a vhost, add the following access_log directive to your vhost configuration file:
access_log /home/nginx/domains/domain.com/log/access_log.json main_json buffer=256k flush=5m;
You can parse JSON logs with jq (pre-installed by Centmin Mod):
jq '.' /home/nginx/domains/domain.com/log/access_log.json
Centmin Mod’s logrotate configuration automatically handles JSON log files alongside the standard access and error logs.
For more details, see the forum discussion.
Cloudflare Custom Logging in nginx.conf http{} Block
These custom log formats are only useful if your server is behind the Cloudflare proxy. They capture Cloudflare-specific HTTP headers that are not present in direct connections.
When running behind Cloudflare, you can define custom Nginx log formats in /usr/local/nginx/conf/nginx.conf inside the http{} block to capture Cloudflare-specific headers like CF-RAY, CF-Connecting-IP, and SSL/TLS details. Centmin Mod’s built-in main_json log format already includes CF headers ($http_cf_ray, $http_cf_worker, $http_cf_request_id, $http_cf_railgun), but you can also create focused custom formats for specific analysis needs.
Important: Add custom log_format definitions to /usr/local/nginx/conf/nginx.conf inside the http{} block. Do not add them inside a server block.
# Cloudflare custom log format with CF-RAY, real IP, and SSL info
log_format cf_custom '$http_cf_connecting_ip - $remote_user [$time_local] '
'"$request" $status $body_bytes_sent '
'"$http_referer" "$http_user_agent" '
'$http_cf_ray $http_cf_ipcountry $ssl_protocol $ssl_cipher';
# Extended format with request timing
log_format cf_custom2 '$http_cf_connecting_ip [$time_local] "$request" '
'$status $body_bytes_sent $request_time '
'$http_cf_ray $ssl_protocol/$ssl_cipher';
# Minimal format for high-traffic analysis
log_format cf_custom3 '$http_cf_connecting_ip $http_cf_ipcountry '
'$status $request_time "$request_uri"';Then use the format in a vhost or server block:
access_log /home/nginx/domains/domain.com/log/cf_access.log cf_custom;Analyzing SSL/TLS Protocol Versions from Cloudflare Logs
Use awk to extract and analyze $ssl_protocol and $ssl_cipher fields from the cf_custom log format to identify TLS version distribution across your traffic:
# Count requests by country (using cf_custom format)
awk '{print $NF}' /home/nginx/domains/domain.com/log/cf_access.log | sort | uniq -c | sort -rn
# Analyze SSL/TLS protocol versions
awk '{print $(NF-1)}' /home/nginx/domains/domain.com/log/cf_access.log | sort | uniq -c | sort -rn
# Find slow requests (request_time > 1s) using cf_custom2 format
awk '$6 > 1.0 {print $0}' /home/nginx/domains/domain.com/log/cf_access.logFor processing compressed (rotated) log files, see Processing Compressed Logs.
For more details and discussion, see the community forum thread.
Configuration Error Checking
Always test your Nginx configuration before reloading:
# Test configuration syntax
nginx -t
# Reload after successful test
ngxreload
# Or restart
ngxrestart
Password Protect a Directory or File
Centmin Mod includes the htpasswd.sh tool at /usr/local/src/centminmod/tools/htpasswd.sh for creating HTTP Basic Authentication password files.
Create a password file with a username and password:
htpasswd.sh create /usr/local/nginx/conf/htpasswd user1 pass1
Then add an auth_basic block to your Nginx vhost configuration to protect a directory:
location /protected/ {
auth_basic "Restricted Access";
auth_basic_user_file /usr/local/nginx/conf/htpasswd;
}
To protect a specific file (for example, a WordPress login page):
location = /wp-login.php {
auth_basic "Restricted Access";
auth_basic_user_file /usr/local/nginx/conf/htpasswd;
# ... existing fastcgi directives
}
After making changes, test and restart Nginx:
nginx -t && ngrestart
For more details, see the forum discussion.
Adding/Enabling Modules
To enable or disable Nginx modules:
- Edit
/etc/centminmod/custom_config.inc - Set the module variable to
'y'(enable) or'n'(disable) - Run centmin.sh menu option 4 to recompile Nginx, or set variables before initial Centmin Mod installation
# Example: Enable ModSecurity WAF and HTTP/3 QUIC
NGINX_MODSECURITY='y'
NGINX_QUIC_SUPPORT='y'
# Example: Enable GeoIP2 Lite
NGINX_GEOIPTWOLITE='y'
Key Configuration Files
| Path | Description |
|---|---|
| /usr/local/nginx/conf/nginx.conf | Main Nginx configuration |
| /usr/local/nginx/conf/conf.d/ | Virtual host configuration files |
| /usr/local/nginx/conf/dynamic-modules.conf | Dynamic module loading directives |
| /usr/local/nginx/conf/phpfpmd/ | PHP-FPM upstream configurations |
| /etc/centminmod/custom_config.inc | Persistent custom settings (survives updates) |
| /usr/local/nginx/modules/ | Dynamic module .so files |
Need help?
Join the community forums for Nginx configuration help and optimization tips.